When it comes to malware, no other type is as infamous as that of a rootkit, and for good reason. This type of malware is capable of embedding itself into a computer’s operating system so well that most users won’t be able to tell the difference. And to make matters worse, it can be extremely difficult to get rid of once it has infiltrated a system.
Now that wouldn’t be so bad if not for the fact that rootkits can be used to gain unauthorized access to a system and cause serious damage to one’s security and privacy. With this in mind, everyone needs to get a good grasp of how it works and what can be done to shield yourself against this malicious threat.
That’s where this quick guide comes in, and we’ll cover everything from what rootkits are, their various types, and what you can do to keep yourself safe. So, let’s get right to it!
What exactly is a Rootkit?
Now, first things first — what exactly is a rootkit?
In a nutshell, a rootkit refers to a class of stealth malware purposefully designed to bypass the security features on a target computer and wrestle control from its users. This makes them particularly dangerous since they can compromise the security of a device/computer without even realizing it.
After a rootkit infects a computer, cybercriminals can use it for nefarious purposes like stealing personal information or even hijacking the system to hurl cyberattacks on other devices. To make matters worse, rootkits can also make subtle changes to an infected system that renders it vulnerable to more dangerous types of malware (ransomware, spyware, trojans, etc.)
So no matter their purpose, rootkits are capable of significant damage to one’s personal data and the system it infects. This highlights the importance of understanding how this type of malware works and what you can do to protect yourself against it.
How does a rootkit work?
Without getting too technical, rootkits use various techniques to gain access and control of a system. This includes taking advantage of vulnerabilities in the target’s OS, adding malicious codes to system files, modifying registry entries, or even hijacking the target computer’s BIOS (basic input/output system). It all depends on the type of rootkit used and the perpetrators’ goals.
In the case of user-mode rootkits, they often infect systems through malware installations, while Kernel-mode rootkits typically use drive-by downloads (malicious codes that are downloaded and executed automatically after visiting a webpage) or physical access hacks.
Among the most infamous example of a rootkit attack is the Stuxnet worm, which devastated Iran’s nuclear installations in 2010. That rootkit was remarkable because it’s one of the first to combine kernel and user-mode rootkit capabilities to infiltrate and override control of target systems. It also used advanced propagation techniques like zero-day exploits and file-less infections to spread across networks of machines — a feature that made it even more dangerous and difficult to detect.
An investigation of the Stuxnet worm revealed the use of stolen private key certificates from the Taiwanese company RealTek, which allowed the attackers to sign their malicious code and bypass security checks. With these stolen certificates, they could also bypass the digital signature checks used to verify legitimate software.
Types of rootkits
A rootkit is a stealthy type of malware that hides inside your Mac and allows bad actors to gain access to your device without your knowledge. Once installed, it is embedded on your system at a deeper level and evades detection. Rootkit malware is dangerous because it conceals malicious activities like setting up backdoors to allow attackers to access your system at any time, setting up keyloggers to steal passwords and enabling remote control of your Mac.
You don’t usually see a rootkit infection coming. More often, it takes advantage of small lapses, an ignored patch, an outdated version, or a convincing email attachment. Exploit kits are built to scan for these weaknesses automatically. Malicious downloads and fraudulent update messages are frequent delivery methods. A compromised shared drive can also introduce rootkit malware without any clear warning.
Rootkits are not all built the same. These categories show how deeply they embed themselves in your system:
- User-mode rootkits run inside regular applications. They pretend to be legitimate software and hide files or processes from you.
- Kernel-mode rootkits reside at the core of macOS. Because they interact directly with system functions, they are much harder to identify and remove.
- Bootkits infect the start-up routine (load before macOS fully starts). They do not go away even after reboots.
- Firmware rootkits attack the firmware of the system rather than the operating system. They are rare and very difficult to remove.
- Memory-based rootkits only live in RAM. They disappear following a reboot but are still able to do some malicious things while the system is running.
Warning signs that your machine may have a rootkit or rootkit virus
Rootkits are designed to stay hidden, but certain warning signs can point to a problem:
- Your Mac suddenly runs more slowly for no clear reason.
- Security software stops working or won’t open.
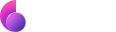
- Unknown processes appear in Activity Monitor.
- Your browser shows random pop-ups or redirects.
- Your system crashes more often than usual.
- You experience unusual outbound network activity.
- Settings are changed without your permission.
These are not the only indicators of a rootkit infection, but they should be checked carefully.
How to detect a rootkit
Unlike ordinary malware, rootkits are built to hide within the system itself. That makes spotting them more complicated than running a basic scan.
Start with a malware scan
A dedicated rootkit scan can go deeper than a basic antivirus check and may reveal threats that standard tools overlook.
A specialized rootkit detector or Mac rootkit scanner is designed to detect rootkits that operate beyond surface-level files. On macOS, professional tools such as Moonlock’s malware removal solution can check for rootkit malware without interfering with essential system components.
Do a deeper scan
Some advanced utilities include a rootkit revealer that compares low-level system data with what macOS reports. Differences could indicate concealed malware.
Check system behavior
Activity Monitor can be used to watch for unusual processes, network traffic, and integrity settings. However, manual checks may still fail to detect kernel-level or firmware rootkits.
How to remove a rootkit
Rootkit removal may be difficult, particularly where the malicious software is deeply entrenched. Here are a few ways to go about this process.
Get rid of the rootkit automatically
Using a professional malware removal solution, such as Moonlock, can help remove rootkit infections safely. Run a deep system scan, review the detected threats, and follow the prompts to remove rootkit components without damaging essential system files.
Here is how to remove a rootkit easily:
- Sign up for your free 7-day trial of Moonlock.
- Open the app and select Malware Scanner.
- Choose Deep Scan to check your Mac for rootkits.
- Click Scan to start scanning.
- Select any detected malware and click Remove.

Restart in Safe Mode
Safe Mode restricts startup programs, which may prevent the loading of user-mode rootkits and make their removal easier.
Reinstall macOS
Where the kernel-mode or bootkits are present, a reinstall of macOS might be required. Firmware rootkits may require additional steps.
Restore from a clean backup
If you have a backup from before the infection, you can restore your device from before the infection to remove the rootkit. Always ensure that the backup is clean.
What can I do to prevent rootkits from infecting my computer?
Prevention is often said to be the best solution to any problem, and the same can be said about rootkit infections. With that said, here are a few best practices that you can start implementing to keep rootkits at bay:
- Make sure that your operating system is always up to date. The same goes for all the apps/software that you’re running on your computer. This one practice alone can safeguard you from the majority of rootkit attacks.
- Use your anti-virus program to run a full scan on your computer at least once a week and keep it updated with the latest virus definitions. If you can automate both processes, then all the better.
- Watch for phishing emails and attachments.
- Enable the built-in security features of macOS, and Moonlock’s Security Advisor can help you with that.
- Use strong, unique passwords.
- Avoid downloading anything from untrusted sources. This is the most common method by which rootkits infiltrate a computer system.
- Insulate your connection to reduce exposure.
But suppose you’re truly serious about keeping your computer safe from rootkits. In that case, we recommend taking your online security to the next level by using a good VPN (Virtual Private Network) service. VPNs help protect against rootkits by encrypting your internet traffic and routing it through a secure tunnel. This makes it practically impossible for rootkits to gain access to your computer.
And you can start doing that with ClearVPN — a VPN service that is simple, secure, and lightning-fast. ClearVPN allows you to instantly access your desired content while protecting your computer from rootkits and other online threats.
Here’s how to get started:
- Go to the ClearVPN website, and click on the “Download for free” button. This will download the ClearVPN installer on your computer. Also, you can download the ClearVPN app from the App Store or other stores for your device.
- Run the downloaded file and follow the instructions to complete the installation process.
- Once installed, launch ClearVPN and create an account (you can do this for free with limited features). You can then log on to the VPN service using your account information (email address and password).
- Select “Smart Connection” for protection.
- Under “Pick Priority”, select “Top Protection“.
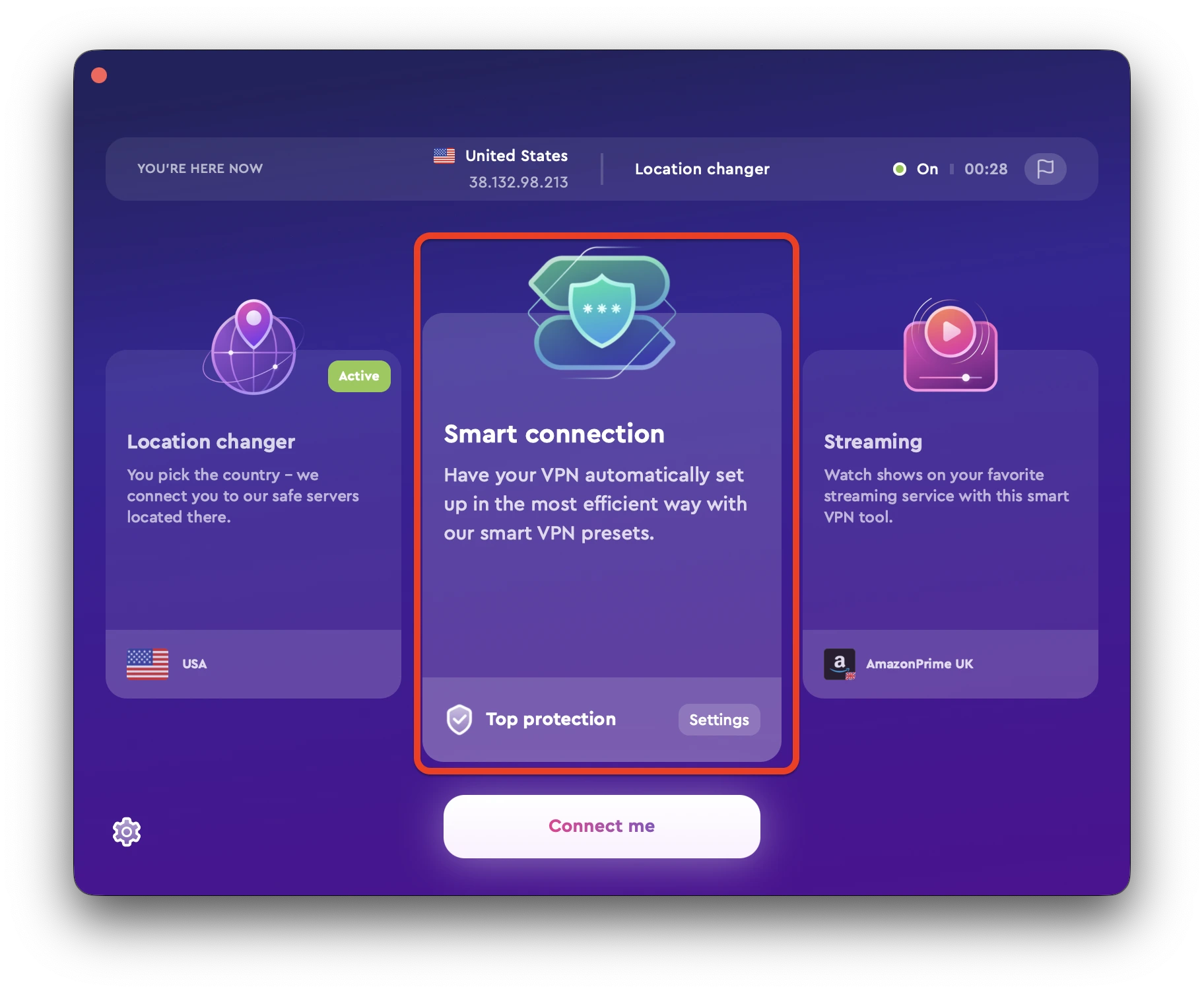
And that’s it — your connection is now secure and safe from rootkit attacks! Keep these best practices in mind, and you’ll be able to drastically reduce your chances of becoming a victim of rootkit malware.