Have you inadvertently clicked on a phishing link and now dread the consequences? It’s definitely not a situation to take lightly, but don’t fret. The good news is you can take actions to mitigate, if not completely prevent, the potential damages.
That’s where this guide comes in! We’ll walk you through specific steps you can take to regain control of the situation.
Why clicking on a phishing link is so dangerous?
It’s important to understand that phishing attacks are far from rare. In 2025 alone, there were an estimated 3.8 million phishing attacks, with most of them using social media and emails to attack.
As for successful attempts, over 90% of successful cyberattacks start with or involve phishing links or emails. For businesses, a single phishing attack is estimated to cost around $4.88 million, with business email compromises costing a total of $6.3 billion in losses.
What’s worse is that phishing attacks likely cause more damage than reported. That’s especially the case for attacks targeting individuals or small businesses where reporting and cyber forensics aren’t feasible options.
There’s no limit to how sophisticated a phishing attack can be. While some rely on lazy templates, others go as far as to use spyware and adware to deceive their victims by using their own information against them.
Nowadays, many phishing emails appear almost indistinguishable from the legitimate organizations they purport to be. They could imitate anything from credit card companies to online stores. They all share the same sense of urgency, designed to make you act before you can consider the consequences.
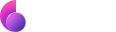
Consider this example of a phishing email designed to steal the victim’s credentials for their Paypal account.
Notice how the email tries to scare the recipient into taking a particular action. Well, that one action is all that phishers need to start siphoning off sensitive information from the potential victim’s online accounts. This includes credit card numbers, email logins, social media accounts, etc.
As you might imagine, clicking on a phishing link can have devastating consequences. It gives cybercriminals all the information they need to execute identity theft and myriad related scams. But beyond financial losses, phishing can cause irreparable damage to one’s personal and professional reputation.
For example, you clicked on a phishing link, so the perpetrator can now access your email. This means the phisher can now impersonate you and email people in your contact list.
How AI phishing changes the game
Before AI, scammers had to either craft their own schemes or use tired templates found on sketchy websites and forums. However, due to several factors, including AI, phishing attacks are becoming more convincing and harder to detect, especially for older and less tech-savvy users.
Generative AI can write highly personalized emails and social media messages that closely mimic real writing styles, tone, and context. And unlike old-school phishing emails, you’re unlikely to find grammatical or spelling mistakes in them.
Some scammers even use AI to generate voice or video impersonations to pose as colleagues or family members. Often, these are nearly indistinguishable from legitimate conversations.
How to recognize a phishing link
You can still avoid phishing attempts by learning to recognize the signs of phishing links. Here are a few helpful guidelines:
- Inspect the URL: Hover your cursor over a link before clicking and look for any misspellings or extra characters.
- Check the domain name: Fake links look nearly identical to authentic ones. They might include additional letters or replace an O with a 0 to evade detection.
- Verify the sender: Double-check the email address you received the email from. Is this address the same one used for previous communications? If in doubt, don’t hesitate to send your own email to check.
- Avoid unsolicited attachments or links: If you didn’t ask for an email attachment or a link from the sender, avoid clicking on them or downloading any files.
- Watch out for urgent messaging: Phishing emails typically want you to click a link, download a file, or perform an action as quickly as possible. If the email sounds unusually urgent, chances are it’s a fake.
What happens if you click on a phishing link?
At this point, you might be wondering what exactly happens after you’ve clicked on phishing email. Here are a few typical scenarios:
- Data harvesting: After clicking on a link, would-be victims are redirected to a page that looks similar to a legitimate source they trust. So that they then willingly enter their login credentials going straight to the phisher.
- Malware distribution: Phishers can use the link to deliver many sorts of malware on a victim’s device. The malware is often a type of spyware designed to steal sensitive data in the background, also known as ransomware.
- Sleeper attacks: Malicious code is introduced to the victim’s device with no noticeable effects at first. However, this type of phishing attack is the most dangerous as it stays with the victim for months, stealing huge amounts of data over a long period of time.
- Session hijacking: Attackers can bypass your password and 2FA altogether by targeting your active session cookies. Your account won’t be able to alert you to the login because it still thinks it’s just you resuming browsing.
- Email account compromised: If attackers gain access to your main email account, they can use it to reset the passwords on all accounts connected to it. It’ll also be nearly impossible for you to recover these accounts without access to your email.
The methods above are but a few examples that outline the sort of damage a phishing attack can cause to your personal or professional life. We cover this not to scare you, but to drive home the fact that it’s a threat every internet user really should take seriously.
Fortunately, there are plenty of things that you can do to avert this disaster, as long as you act fast enough. In the next section, we’ll review a step-by-step playbook you can implement in response to a suspected phishing attack.
What to do after clicking a phishing link: A step-by-step approach
If you clicked on a link before you realized it was a phishing link, you can still work to minimize the damages but only if you act fast.
Here’s what you should do:
- Immediately close the page. Don’t enter any info or passwords that the page asks of you.
- Disconnect your device from the internet to stop any flow of information.
- Run a malware scan of your Mac. You can use Moonlock to run a deep antimalware scan that’ll look through your device for all sorts of malware, spyware, and even keyloggers to steal your credentials.
- Once you make sure your Mac is clean, back up your data to an external drive to ensure that you have the latest possible version of your personal files.
- Now, it’s safe to reconnect to the internet. Change your passwords on all your accounts, starting with the most sensitive ones. Consider enabling 2FA where it’s available.
- Monitor your accounts, online activity, and financial transactions for the next couple of weeks. If you notice any suspicious actions, act quickly to notify your bank and secure your accounts.
- Report the case to all affected parties, like your employer, if your work email was compromised. You should also report to the Federal Trade Commission and the FBI Internet Crime Complaint Center to help prevent future attacks.
- Learn from the experience. Think about how you got into the situation in the first place and take the events to heart. Remember that the best solution to any problem is to prevent it from happening in the first place.
Again, time is of the essence when dealing with a phishing attack. The sooner you take action and complete the steps above, the greater your chances of minimizing any damage.
How phishing attacks can be prevented?
Now that we’ve covered what specific actions you should take after clicking on a phishing link, what about preventive measures? That requires us to be extra vigilant and take the following precautionary measures in our online activities:
- Update your software and operating system. Cybercriminals often take advantage of new software vulnerabilities. Installing the latest updates from software developers will help prevent these exploits.
- Use passkeys instead of passwords whenever possible. Passkeys are resistant to phishing because they are tied to a specific website or app and can’t be reused on fake domains, making it significantly harder for attackers to steal your login credentials.
- Use a highly rated security software that you can trust with your personal files and online activity, like Moonlock. Designed specifically for Macs, it has real-time protection and the ability to schedule Deep Malware scans to make sure your device is always clean. Give it a shot with a 7-day free trial.

- Spread the word. Tell the people around you about your experience with phishing attacks and how they can protect themselves. Phishing relies on internet users’ general lack of awareness, so the more people who know about it, the less effective it will be.
- Always verify. If there’s one rule of thumb that’ll help keep you safe online, it’s that you shouldn’t take anything you see at face value. Take the time to confirm the source of any messages you receive that entail taking a specific action — clicking a link, downloading a file, etc.
- Strengthen your passwords. Ensure all your passwords are unique and contain a long combination of letters, numbers, and special characters.
- Switch to a secure email service with phishing filters that automatically detect and prevent phishing emails from appearing in your inbox. A few good examples of such email services are ProtonMail and SecureMyEmail.
Make it a habit to back up important data. That way, you’ll always have a way to retrieve them in the case of cyber attacks such as viruses and ransomware.
Of course, if you’re serious about your data security and ensuring you’re protected from phishing attacks, then there’s one other tool we recommend adding to your arsenal — a VPN (Virtual Private Network) service!
VPNs add another layer of data security to your online activities by encrypting all data from your device. This prevents phishers from being able to read any data they can steal from your device. VPNs also conceal your real IP address, which makes it more difficult for cybercriminals to target you with a phishing attack in the first place.
And the best part is that VPNs are now fairly easy to use these days. In fact, many premium VPS on the market will get you up and running in just a few minutes. One good example is ClearVPN — a fast and user-friendly Ukraine-based VPN service that works on all popular devices and operating systems.
Specifically, this includes popular operating systems like Windows and macOS and mobile devices such as iPhones and Android smartphones. All you have to do is download the installer for the VPN app, run it, and connect! Also, ClearVPN now has a free 3-day trial, so you can try to use it for free!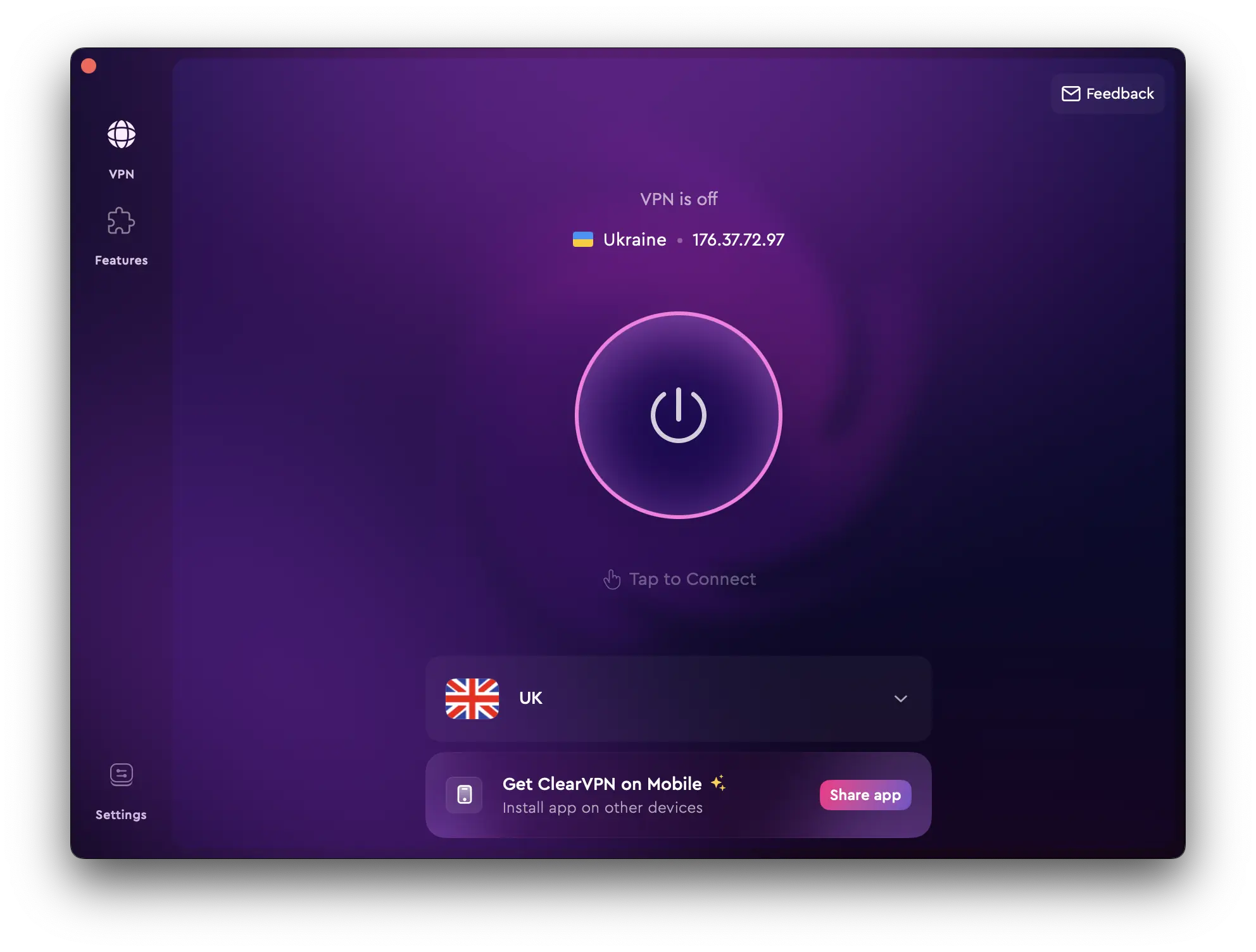
Every bit helps when it comes to preventing phishing attacks. With a good VPN service, you can greatly reduce your chances of becoming the next victim and learn how to reduce damage to your finances and/or reputation.
FAQs
Can you get hacked by clicking on a phishing link?
Yes, it’s possible, especially if you provide sensitive information that a hacker could work with. This includes your date of birth, location or login credentials for any of your accounts. Hackers can use phishing to gather information from their victims covertly.
How do I know if a link I clicked is safe?
One quick way to determine whether a link is legitimate is to review its URL structure carefully. If the domain name does not match the organization it’s supposedly from, it’s likely a phishing link.