Malware is continually advancing, and threat actors are inventing new and clever methods that make it difficult to spot. Fileless malware is one of the latest threats that can stay silent in your system, making it tricky to detect. According to ControlD’s 2026 malware statistics, fileless attacks now account for 70% of all serious malware incidents.
Fileless malware is malicious software that runs in your system’s memory (RAM) and blends in with normal system processes, making it incredibly difficult to find and complicated to remove. The latest security reports reveal fileless malware examples that prove just how sophisticated these attacks really are. Fileless variants in ransomware toolkits alone have increased 40%, and 93% of organizations have experienced at least one ransomware-ready intrusion in the past 24 months
What is fileless malware?
Fileless malware is a type of malicious software that doesn’t rely on traditional methods, such as downloading and installing files, to infect a computer. Instead, it takes advantage of vulnerabilities in existing programs or the operating system to infect a machine.
While fileless malware has been around for years, it has seen a recent uptick in popularity among cybercriminals. One of the reasons for this is that traditional antivirus programs are not designed to detect or block fileless malware, making it a very effective way to infect computers.
One of the most dangerous things about fileless malware is that it’s very difficult to detect. Since it doesn’t rely on files, traditional antivirus programs are ineffective against it. Fileless malware can also avoid detection by using legitimate programs that are already whitelisted by security systems.
Fileless malware is often delivered through phishing emails or other social engineering techniques. Once the malware has been executed, it resides in the system’s memory and starts to collect information or perform other malicious activities.
Notable cases of fileless malware attacks
The numbers above only tell part of the story. Here are some real-world fileless malware attacks from the past year that show how threat actors are putting these techniques into practice.
- In 2025, Microsoft’s researchers identified Storm-0249 as responsible for a phishing-based fileless malware campaign as early as 2024. The threat actor used ClickFix-style social engineering to trick users into running malicious PowerShell commands that executed memory-only malware. This gave them the opportunity to deploy ransomware on the enterprise systems they targeted.
- In February 2026, a stealthy malware campaign known as DEAD#VAX—not to be confused with vaccine safety—delivered a remote access trojan as a payload (AsyncRAT) using IPFS-hosted VHD phishing files to discreetly take over a victim’s system without notice, all done remotely. Heavily obfuscated scripts were used to perform fileless malware injection into legitimate Windows processes, making it very hard to spot because it blended in with them.
- In 2025, security researchers at Wiz identified an unknown threat group that spearheaded a fileless cryptomining campaign to stealthily mine cryptocurrency in over 1,500 misconfigured and publicly exposed PostgreSQL servers, which affected victims’ computing resources. The activity was linked to the threat actor JINX-0126, previously flagged by Aqua Security for abusing built-in database commands to execute memory-only malware without writing any files to disk.
How to detect and remove fileless malware
Fileless malware is very tricky to find, considering that it is hidden on a kernel level in the system memory and can appear as a normal system process. Since it doesn’t use files like most malware does, there are none to scan, which makes it increasingly difficult for antivirus tools to scan and detect. However, there are other methods you can use to find and eliminate memory-only malware.
Detecting fileless malware
The signs are subtle, but they’re there if you know what to look for.
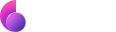
Monitor unusual system behavior
If your system is acting strangely or more sluggish than usual, see if you notice any commands are running in the background (e.g., PowerShell, Activity Monitor, or Terminal). Also, check for unfamiliar processes in your system activity monitor that are using up a lot of your CPU. If you find anything odd, investigate it immediately.
Use a real-time endpoint detection and response monitoring (EDR) tool
A real-time endpoint detection and response (EDR) tool goes beyond signature-based antivirus by analyzing behavior instead of just scanning files. It tracks process chains (how scripts and commands execute across the system), monitors memory-level activity where fileless malware operates, and uses anomaly detection to flag suspicious patterns in real time. This allows EDR to identify attacks that never touch the disk, such as PowerShell abuse or in-memory injection, which traditional antivirus tools often miss.
Scan memory for hidden activity
Most AV tools and antimalware solutions focus on scanning files stored on the disk. Fileless malware requires a different approach. Use dedicated memory scanning tools that analyze running processes and system RAM to detect injected code that never touches the disk. These tools inspect live process behavior and memory regions to uncover hidden or unauthorized execution in real time.
Check logs for scripts and command activity (PowerShell or Terminal)
You can enable logging of scripts and commands to see what’s behind the scenes to get to the root cause of suspicious or hidden activity.
For Windows users:
- Enable PowerShell Script Block Logging
- Turn on Module Logging
Mac and Linux users can manually log shell activity or review command history and system logs in the command line.
Getting rid of fileless malware
Since fileless malware lives in memory, the removal process looks a little different from dealing with a typical virus. Act quickly and follow these steps.
Disconnect your computer from the internet immediately
This step cuts your system’s communication to any dangerous servers that may remotely control your device or send commands, and it helps prevent further fileless malware from spreading to other devices or networks. Here’s how to do it:
- Unplug the Ethernet cable (if applicable).
- Turn off Wi-Fi.
- Disable Bluetooth, AirDrop, or file sharing as necessary.
Shut down any suspicious operations or processes
Turn off anything that is running that shouldn’t be. Use security tools as needed.
Restore your system from a clean backup
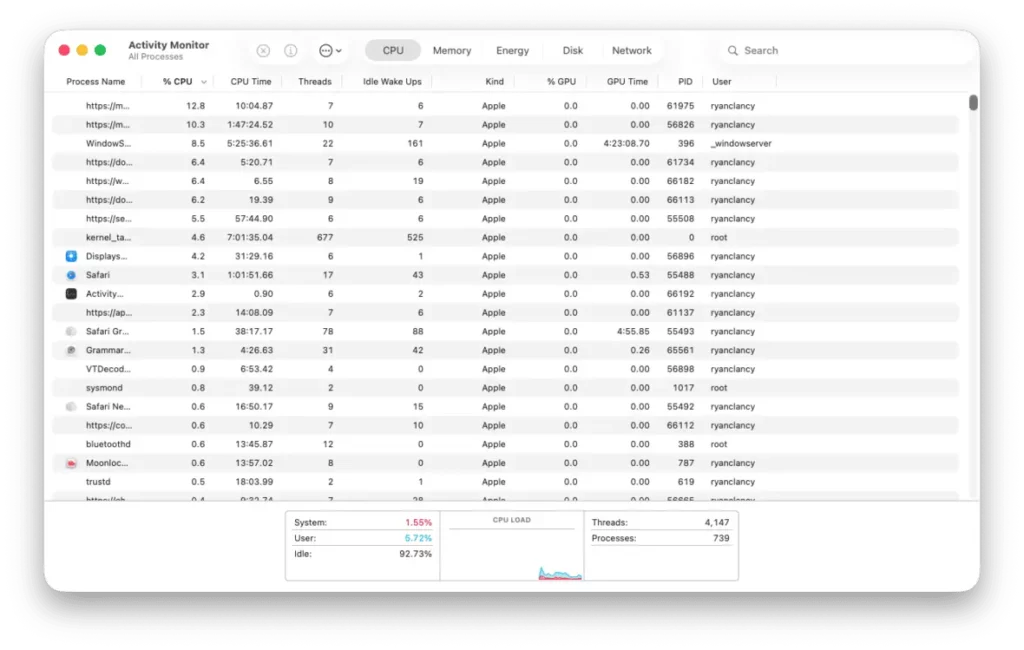
Restoring from a backup taken before the infection is the most reliable way to eliminate fileless malware, including any persistence mechanisms it may have embedded in registry keys or scheduled tasks. Once restored, use Moonlock’s System Protection to check that your macOS security settings are properly configured before you reconnect to the internet — so you’re not jumping back online with the same gaps that got you infected in the first place.
Secure all your accounts and remove any access to them
Assume that access to your accounts has been compromised and your passwords have been stolen. Change all your passwords to secure ones immediately and store them in a trusted and secure password manager. Additionally, end all sessions and revoke any unauthorized access to your accounts.
Seek help from a malware security expert for complex needs
If you still have trouble detecting or removing fileless malware, hiring a malware security expert to help you is never a bad idea. These threats can indicate a deeper compromise, and an expert can help ensure that nothing is missed.
How to protect against fileless malware
Be proactive by reducing the opportunities that attackers can exploit to infect your system. This is imperative for fileless malware protection. Do the following.
Keep systems and software updated
Operating systems and apps that aren’t up-to-date can leave vulnerabilities that threat actors can exploit. To prevent this:
- Update your system and apps routinely.
- Patch anything that connects to the internet.
- Remove any unsupported or unneeded software.
Build a layered malware defense
No single tool can fully protect you from every threat out there — not from fileless malware, ransomware, spyware, trojans, or any other type of attack. A layered approach is the only reliable way to stay ahead, combining good habits with the right security software.
Moonlock adds real-time protection against malware and monitors your system around the clock for suspicious activity. Its Security Advisor guides you through safer online habits, while System Protection checks your macOS settings and flags anything that needs tightening — so your defenses aren’t just active, but properly configured. Try Moonlock free for 7 days and see how much stronger your Mac security can be.

Disable macros in documents
Macros can trigger scripts that execute fileless malware. Because macros can run embedded code directly in memory (often via tools like PowerShell), they are a common entry point for fileless attacks that never write anything to disk. Here’s what to do:
- Disable macros by default.
- Only allow trusted macros.
- Use Protected view.
Restrict PowerShell usage
PowerShell is commonly abused for fileless malware injection. It’s wise to take the following precautions:
- Set restrictive execution policies. This means limiting which scripts can run on your system. For example, blocking unsigned or untrusted PowerShell scripts and only allowing those from verified sources reduces the risk of malicious code executing in memory.
- Turn on script logging.
- Limit who can access it.
Enforce least-privilege access
- Remove admin rights from anyone unauthorized.
- Let users access only what their role requires.
- Give higher access only when needed, then remove it.
Phishing awareness
Most fileless malware attacks rely on social engineering. Keep the following in mind:
- Be cautious of suspicious messages and links.
- Verify before clicking.
- Avoid unexpected downloads.
Enable application control (allowlisting)
Allowlisting blocks unauthorized scripts and apps:
- Allow only approved programs.
- Block unknown scripts.
- Restrict execution from temporary folders.
Keep backups of your important data
Backups help you recover your files if something goes wrong:
- Save copies in a safe place, like a cloud or external drive.
- Make sure you can get your files back when needed.
- Keep your backups separate from your main account.
When it comes to fileless malware protection, it is well worth pointing out that its spread primarily through social engineering. Cybercriminals will use various methods in order to trick users into installing the malware onto their systems.
This is why it is important to exercise caution when opening email attachments or clicking on links from unknown sources. In addition, you should always keep your operating system and other software up to date as this can help close any vulnerabilities that could be exploited by fileless malware.
It is also a good idea to back up your data on a regular basis. This way, if your computer does become infected with fileless malware, you will not lose any important files or data.
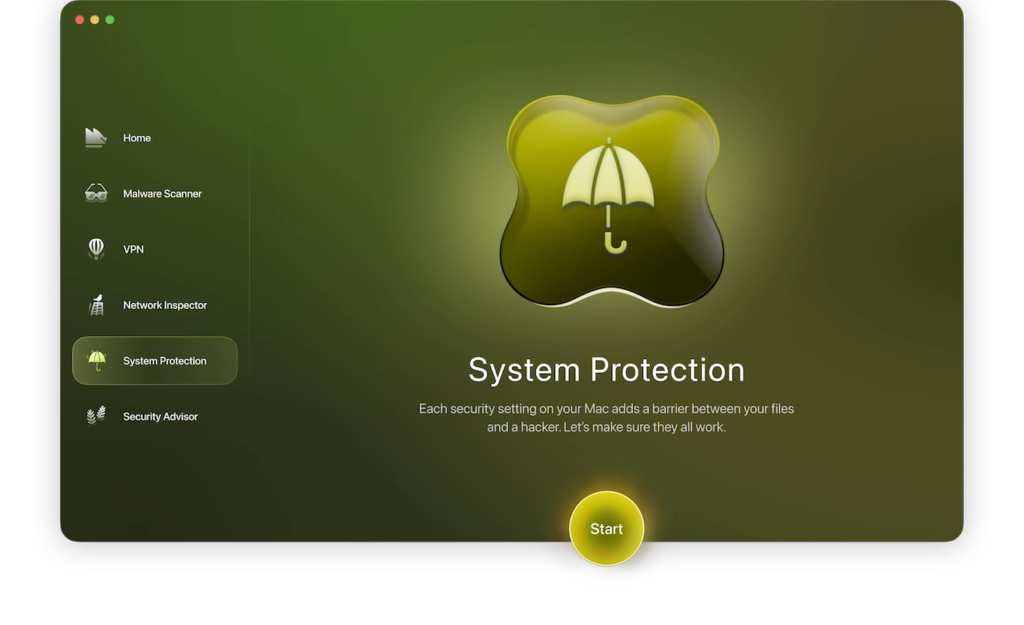
And finally, you should consider using a VPN (Virtual Private Network). This will encrypt your traffic and help to protect your privacy online. Using a VPN can also help to prevent fileless malware from infecting your system as it will make it more difficult for cybercriminals to target you.
Of course, not just any VPN will do. You should make sure to choose a reputable VPN service that uses strong encryption and has a good privacy policy. We recommend ClearVPN as it meets all of these criteria and more. Plus, it’s extremely easy to use, with one-click shortcuts that will make it a breeze to connect to the fastest server available. Download ClearVPN app and protection and privacy in a click. Here is how to do this:
- Download and install ClearVPN app on you device.
- Run the app and log in to the app.
- Choose Smart Connection mode and click on “Connect me” button – That’s all, now your connection is protected from most of the cyber threats.
FAQs
How does fileless malware work?
Fileless malware usually starts with some sort of social engineering attack in which the user is tricked into executing a malicious payload. Once the payload is executed, it will use legitimate programs and system resources in order to infect the computer.
How can I protect myself from fileless malware?
There are a few things you can do in order to protect yourself from fileless malware. Firstly, you should exercise caution when opening email attachments or clicking on links from unknown sources. In addition, you should keep your operating system and other software up to date in order to close any vulnerabilities that could be exploited by fileless malware. Finally, you should consider using a reputable antivirus program that offers protection against this type of malware.
What should I do if my computer is infected with fileless malware?
If your computer is infected with fileless malware, you can try using a specialized tool to remove it. Alternatively, you could try using a system restore point to return your computer to a previous state before the infection occurred. However, this method is not always effective and may not work on all types of malware.