Computers have become an integral part of our lives. We have come to rely on them for entertainment, communication, business operations, and even medical care. But like anything else, computers can be used for more criminal purposes. One of the most concerning cyber threats is computer worms, and if you don’t understand what they are and how to protect yourself from them… you could become a victim.
How does a computer worm work?
A computer worm is a kind of malicious software (malware) that replicates itself and spreads from one system to another without human interaction. It can enter your system via email, instant messages, file transfers, or websites.
A PC worm works by exploiting security vulnerabilities in an operating system or application. Once it has infiltrated a computer, it will replicate itself and spread to other computers on the same network. It can also use networks of infected computers (called “botnets”) to launch coordinated attacks against targeted systems.
What’s the difference between a computer virus and worm
A common misconception is that a worm is the same thing as a computer virus.
While both are malicious programs, there is an important distinction between them: a virus must be manually attached to an existing program in order for it to spread, whereas a worm can replicate itself and spread without any user action required.
For example, a virus might be attached to an email attachment, but email worms can spread by automatically sending copies of themselves from the infected machine to other machines on the same network.
Different types and classifications of computer worms
Unlike trojans, which do not replicate and require user interaction, a computer worm is malware that spreads by copying itself and often doesn’t require a host or user interaction. It moves automatically across systems through different vectors and is classified based on how it spreads.
Computer worms come in several different types:
- Email worms: Email worms tend to spread through infected attachments or bad links. After they’re opened, they are able to forward themselves to Gmail, Outlook, or company contacts.
- File-sharing worms: These propagate on peer-to-peer (P2P) networks and torrent sites that carry pirated software, games, music (such as Napster in the 90s), and films.
- Network worms: Network worms scan the public internet, searching for vulnerable systems, and exploit automatically unpatched software. Some of the most notable ones are the Morris Worm and WannaCry.
- Internet worms: Similar to network worms, internet worms scan the web to locate vulnerable systems and attack them by exploiting unpatched software or poor settings. They do not require any user intervention.
- Messaging worms: These worms spread through malicious links once opened that are sent via chat apps or iMessage.
- IoT worms: IoT worms attack routers, smart cameras, smart TVs, and other “internet of things” devices to exploit default credentials and unpatched firmware. Mirai, which infected thousands of devices globally to build massive botnets, is the perfect example.
- Mobile worms: These worms attack smartphones and tablets and are spread with malicious applications via SMS links or messaging platforms. More commonly seen on Android, these are rarely seen on iOS devices.
- USB worms: These worms transfer to external drives such as USBs, hard drives, etc. Once you plug in the infected drive and run the hidden malicious program, the worm spreads to the new computer.
So what does a worm can do to a computer?
Computer worms can do a lot of damage to an infected system. They can corrupt data, delete files, or even give hackers access to confidential information stored on the machine.
For businesses, this could lead to lost productivity, damaged reputation, and severe financial losses. For individuals, the loss of important data or financial information could be devastating.
To give you an idea of the damage a worm can cause, consider the “Love Bug worm” virus of 2000. It caused an estimated $5.5 -8.7 billion in worldwide losses by infecting millions of computers and clogging up corporate networks with its malicious payload.
Common warning signs that your computer might be infected
Worms work quietly in the background while draining resources and leaving subtle clues that they’ve spread. If something feels “off,” don’t ignore it; worm malware often shows itself through small but escalating system changes.
Here are a few ways to tell that your computer may be infected by a worm:
- Unusual spikes in network activity
- Frequent crashes or freezing
- Unknown programs running automatically
- Sudden pop-ups on your browser
- Emails or messages sent from your account without your knowledge
- Security settings changing unexpectedly
Practical ways to detect a suspected worm infection
Think your system has a worm? The sooner you catch it, the less harm it can cause.
These practical steps will help you detect a worm:
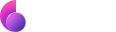
- Look for background processes that eat up your CPU. Go to Activity Monitor on your Mac and scroll up and down to find any processes that are using excessive CPU or memory.
- Audit your installed apps. Look at your Applications folder and remove any programs you didn’t install or that don’t look familiar to you.
- Monitor outgoing network traffic. Use your firewall or router logs to spot unusual outbound connections.
- Run a full security scan. Perform a full system scan to look for malware so you can identify, quarantine, and remove any threats.
How to remove a computer worm automatically
If you suspect your device has a worm, the easiest way to confirm this without spending a lot of time and energy getting rid of infections is by using the Mac security tool Moonlock to remove malware from Mac.
Take these additional steps:
- Get a free trial of Moonlock
- Run a full system scan using a malware scanner.
- Follow the removal instructions provided.
- Restart your device and scan again to ensure that the infection is fully removed.

How to get rid of a computer virus manually on Mac
- First things first: Disconnect your Mac from the network. You can do this by disabling your Wi-Fi connection or removing the Ethernet cable.
- Follow the steps 1 through 4 for detecting a suspected worm infection.
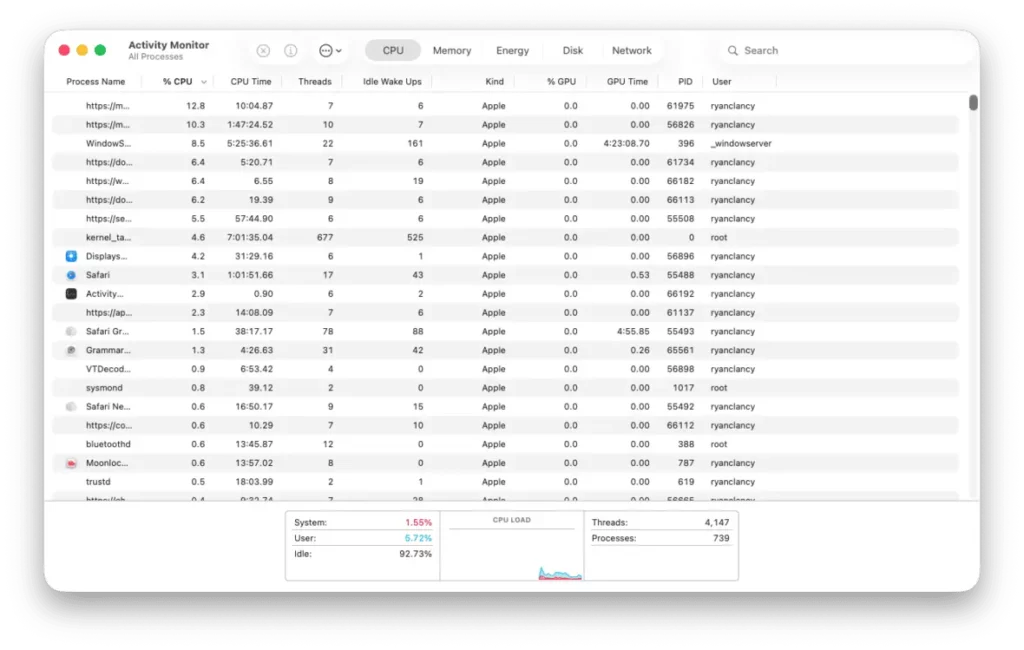
- Head to System Settings, click General, and open Login Items. Once you’re in Login Items, examine the startup list. Remove any suspicious entries immediately.
- Finally, empty the Trash and restart the system. When the Mac boots again, run a deep malware scan with Moonlock to confirm that no harmful files remain.
If you’re unsure how to remove a worm manually, use the Moonlock malware removal tool for Mac or peace of mind.
How to prevent computer worms?
Now that you know how to get rid of a worm, it’s important to also understand how to prevent them in the first place. This can be done by following some simple best practices:
- Keep your computer’s operating system and applications up to date with the latest security patches. This will help close any potential security vulnerabilities that could be exploited by worms.
- Be cautious when opening emails and attachments from unknown sources. Don’t open any attachment that looks suspicious or has a file format you don’t recognize.
- Don’t click on links or popups from unfamiliar websites as they may be malicious in nature.
- Install and regularly update antivirus software with the latest malware definitions.
In addition, you should also consider encrypting any sensitive data that you store on your computer or use when connecting to the internet. This will help protect your personal information from being stolen in the event of a worm infection.
You can do that with a good VPN service like ClearVPN. It encrypts your data and makes it virtually impossible for hackers to access it. Plus, it’s compatible with most operating systems/devices and relatively easy to use.
All that you have to do is run the ClearVPN app on your device and use the shortcut “Smart connection” that can make your connection private and secure in a click.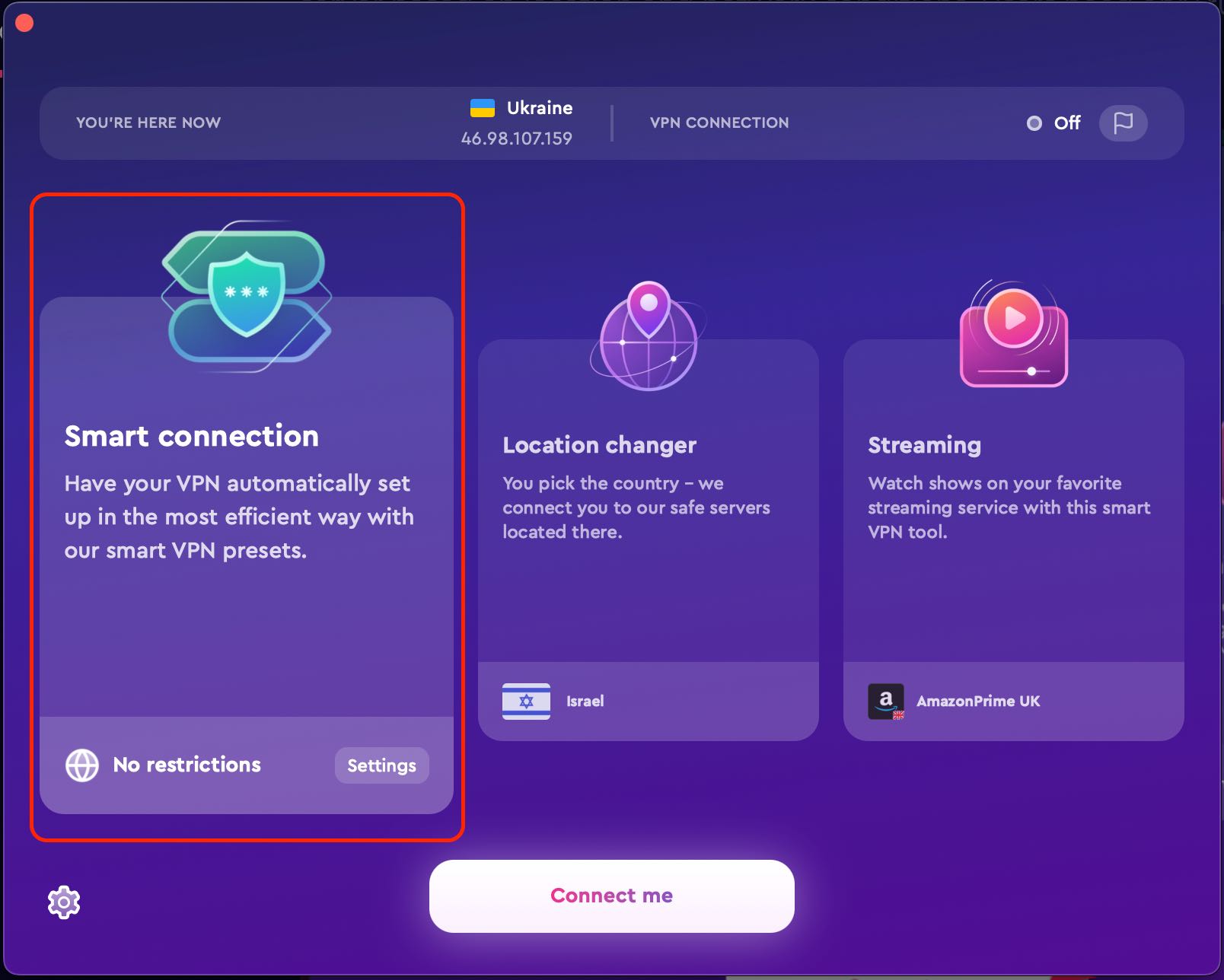
By following these simple steps, you can keep your computer safe and secure from the threat of worms. The best defense is always a good offense when it comes to malware protection. So make sure to stay one step ahead by actively protecting your device against any potential threats.
FAQs
What are the signs of a computer worm infection?
The most common signs of a computer worm infection include sluggish system performance, frequent crashes, sudden pop-ups, or other unexpected behavior
How do computer worms spread?
Computer worms usually spread through emails, downloads, malicious websites, and peer-to-peer file-sharing networks.
How can I protect myself from computer worms?
You can protect yourself from computer worms by keeping your operating system and applications up to date with the latest security patches, being cautious when opening emails and attachments from unknown sources, not clicking on links or popups from unfamiliar websites, and installing and regularly updating antivirus software with the latest malware definitions.
A VPN can protect your device from computer worms by hiding the IP address of your device and encrypting your data. This makes it more difficult for malicious actors to access your system.
By using a VPN, you also limit the ability of hackers to exploit weaknesses in unsecured networks, as they cannot access the data that is being transmitted through the secure VPN tunnel. This will reduce the chances of computer worms entering and infecting your system.
Finally, a VPN can provide additional layers of security by allowing access only to trusted websites and networks. When you connect to a website or network through a VPN, the service acts as an intermediary between you and the website or network, allowing the data to be transmitted securely. This provides an extra layer of protection against dangerous computer worms.