A VPN protects you from hackers. But how does it hide your IP address from cyber criminals, spies, or the government? Is it foolproof, or should you take additional precautions? The answers lie in the technology that drives the VPN tunnel to keep you secure.
In this article, I’ll dive deeper into the technicalities of VPN tunneling and what it means for ordinary users.
What is VPN Tunneling?
A VPN tunnel establishes a secure connection between your device and the internet. Like a physical tunnel, the VPN tunnel creates an impenetrable barrier along the data superhighway that shields communication between a device and the destination server. No hackers or enforcement agencies can spy on the underlying information you send via a VPN tunnel.
All VPN tunnels have two distinct features; encryption and IP masking.
Encryption is a software process that scrambles your data to make it unintelligible for anyone spying on the connection.
Meanwhile, IP masking hides your actual IP address by replacing it with the VPN server’s IP address.
How does a VPN Tunnel work?
If you’re browsing the internet without a VPN, you become a sitting duck for hackers. They identify your device by tracking the IP address and can intercept sensitive data that you send. Likewise, governments and big media monitor civilians on unprotected connections by monitoring their web activities.

Setting up a VPN tunnel puts a stop to unwanted surveillance. It creates an encrypted environment where data exchange can take place securely.
Here’s what happens in a VPN tunnel.
- Data is encrypted before it leaves your device.
- The encrypted data packet goes through the VPN server.
- The VPN server hides your IP address and replaces it with a new one.
- Encrypted data travels from the VPN server to the destination.
- Data is then decrypted when it reaches the web server.
- The process repeats when the web server sends data to your device.
The immediate effect of VPN tunneling is the anonymity it provides users. For example, if you’re connecting to a US VPN server from London, your traffic will appear as originating from the US. This unique capability makes VPN an excellent tool to bypass geo-locational restrictions, such as streaming Netflix US.
VPN tunneling also prevents hackers from misusing data by encrypting them from end to end. Most VPNs use AES-256 encryption, which militaries, banks, and governments use to protect confidential data. It is technically impossible to break the AES-256 encryption without a cipher key, as it would take trillions of years to do so.
What are the common VPN tunneling protocols?
Besides encryption, VPNs rely on tunneling protocols to transfer data securely between devices. To get a better picture, imagine secure VPN protocols like vehicles that move in a tunnel. Some are faster than others, while others have more safety features.
You will likely come across these VPN protocols when using a VPN.
L2TP/IPSec
Layer 2 Tunnel Protocol (L2TP) pairs with the Internet Protocol Security suite (IPSec) to provide dual-layered encryption. It also works well with AES-256, which makes it a popular tunneling protocol among providers. While it provides ample security, L2TP lacks speed because of its double encryption mechanism.
IKEv2/IPSec
The Internet Key Exchange version 2 (IKEv2) is a protocol many VPNs use to establish secure connections on mobile devices. Like L2TP, IKEv2 combines with IPSec to secure data sent from the device. However, IKEv2 is faster due to its inter-device security associations policy.
OpenVPN
OpenVPN was the de-facto standard for VPNs until the faster and more secure WireGuard took over. Like IKeV2, OpenVPN offers formidable speed and security for VPN tunneling. It is also open source, which means experts have continuously vetted and improved the protocol over the years.
WireGuard
WireGuard is the latest and safest VPN encryption protocol. Compared to OpenVPN and IKEv2, Wireguard is faster and more secure, thanks to its smaller code size. WireGuard provides hyper-fast and reliable connections on both mobile and desktop devices.
Which is the best VPN tunneling protocol?
Theoretically, WireGuard is the best VPN protocol for a secure and fast connection. However, factors like hardware, operating system, and server distance affect how different protocols perform. Unless you’re familiar with how each protocol works, choosing the ‘best’ VPN tunneling protocol is challenging.
In such cases, users rely on ClearVPN, which automatically chooses between WireGuard, OpenVPN, and IKEv2 based on what they want to do online. TechRadar experts recommended ClearVPN because they hide the complexities of setting up a VPN connection.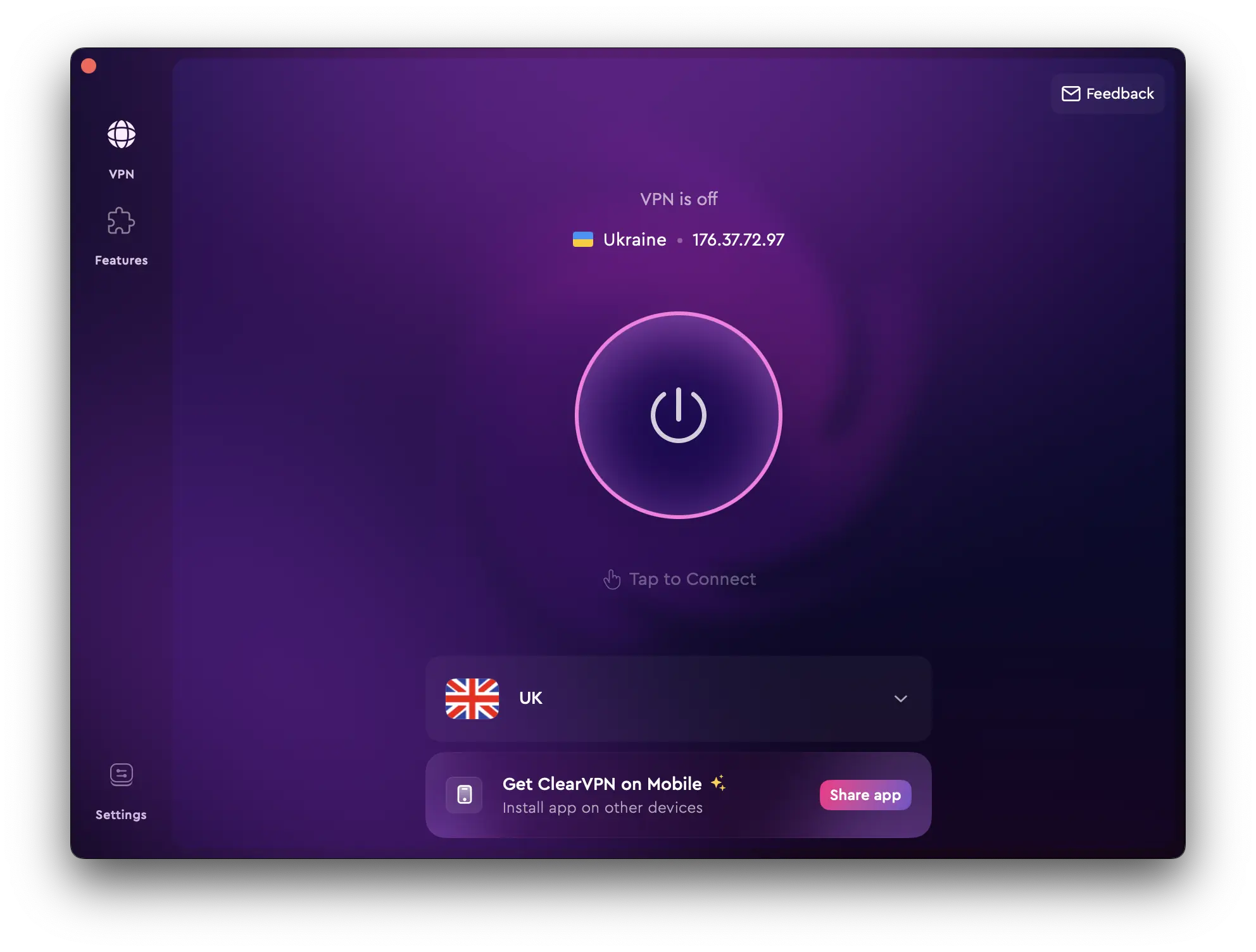
What is VPN Split Tunneling?
Split tunneling allows you to exclude specific applications from using the VPN tunnel. Even with the VPN turned on, these applications send data through an unencrypted internet connection. As such, these applications might be susceptible to hacking attempts.
Still, split tunneling is helpful in certain circumstances. For example, some banking apps don’t work with a VPN. Therefore, bypassing the VPN with split tunneling is the only way to perform financial transactions when using a VPN. Also, some users use split tunneling to prevent data-heavy apps from slowing down the VPN connection.
FAQs
Can a VPN tunnel be hacked?
The short answer is yes if the VPN relies on insecure VPN protocols or unencrypted methods. For example, some free VPNs use the PPTP protocol, which is easily hackable. Cybercriminals might exploit an insecure VPN tunnel and carry out secondary attacks. It’s best to avoid using free VPNs for this reason.
Is a VPN tunnel safe?
Yes, a VPN tunnel is generally safe as it encrypts data transmitted between your device and the VPN server, protecting it from eavesdroppers, hackers, and other potential threats. However, the level of safety depends on factors like the VPN provider’s reliability, the encryption standards used, and how well the VPN is configured. It’s essential to choose a reputable VPN service and ensure it uses strong encryption protocols to maximize security.
What are the advantages of VPN tunneling?
Setting up a VPN tunnel keeps your data safe from those who would like to capitalize on unsecured data transmission. A VPN is also useful when you use public WiFi to send emails, transfer funds, or purchase products online.
What is the difference between a proxy and a tunnel?
A proxy is an intermediary gateway that masks your IP address when browsing the internet. However, it doesn’t encrypt the data as a VPN tunnel does. Moreover, proxies only work for browsers and not apps. If you use an app despite connecting to the proxy, your actual IP address will still be revealed.