When you key in a website’s URL on the browser, you expect it will bring you to a familiar webpage. But sometimes it doesn’t. Instead, you find yourself staring at an ads-filled page or taken to a malicious website. And that’s the result of a successful DNS hijacking. This guide will explain DNS hijacking, why it matters, and how to stay protected against such attempts.
What is DNS and an IP address?
DNS, or Domain Name Server, is a special computer that stores a list of domain names and their corresponding IP address. A domain name is the website’s name that users key in on the browser’s address bar.
Meanwhile, an IP address is a unique string of numbers that points to the web server’s location on the internet.
For example,
- facebook.com is a domain.
- 2a03:2880:f12a:83:face:b00c:0:25de is Facebook’s IP address in the IPv6 format.
When you enter a domain name, the DNS finds the matching IP address for the browser. Then, the browser sends subsequent data requests to the IP address.
In real life, a DNS lookup may involve several DNS servers before returning the web server’s IP address.
How does DNS hijacking work?
DNS hijacking is an intentional attempt to return the wrong IP address when a browser sends a query. Instead of landing on the right website, the perpetrator intercepts or redirects the query to trick your browser into displaying the wrong website. This is a common practice that hackers, ISPs, or governments use to compromise or interfere with your browsing experience.
For example, you want to visit an online banking website but are redirected to a fake website that steals financial data. Or an ISP might divert users to ads-filled webpages when they enter unregistered domain names. Meanwhile, some governments use DNS hijacking to censor websites their citizens visit.
Types of DNS hijacking attacks
DNS hijacking, or DNS spoofing, happens in several ways.
Malware
In this attack, perpetrators infect the user’s computer with malware and, subsequently, affect its DNS configuration. This reroutes the web query to a fake server, leaving the user vulnerable.
Router DNS attack
This is a DNS hijacking attack that targets home routers. Cybercriminals gain access to the router and change its DNS settings. As a result, all devices connected to the router fall victim to the attack.
Man-in-the-middle attack
Instead of redirecting to a visually-different website, perpetrators send users to a similar-looking one. Man-in-the-middle attack intend to trick users into believing that they’re on the real website.
DNS server attack
Some DNS hijacking attacks target the DNS servers by altering the DNS records that map domain names to IP addresses. Such attacks are also known as DNS poisoning.
Compromised web server
Hackers might also gain access to a web server and change its DNS configurations. In such an event, the web server redirects the users to another website without the owner’s permission.
ISP DNS Spoofing
In some cases, the ISPs are the culprit behind DNS spoofing. They intercept specific outgoing requests and redirect users to advertisements.
How to detect DNS hijacking?
DNS hijacking often happens unbeknownst to users. You may be the victim of intentional DNS redirection without noticing any tell-tale signs. However, there are ways to find out if you’re a target of a DNS attack.
Ping a non-existent domain name.
- Open the command terminal and ping the URL.
- For example, “ping pwerasd.com”..
- The terminal should return an unsuccessful message. If it returns successful pings, it’s a sign of DNS hijacking.
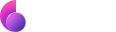
Use Online DNS Checker
- Visit https://whoismydns.com
- Check the owner of the DNS server.
- If you don’t recognize the DNS owner, you might be a victim of DNS hijacking.
Check your router
1. Log in to your router’s admin page and check the DNS settings.
2. Alternatively, use a DNS checker software for routers and scan for altered DNS configurations.
How to prevent DNS Hijacking?
DNS hijacking may seem like a harmless trick for displaying unsolicited ads. But such attacks can result in monetary losses, identity theft, and other serious consequences. Follow these methods to prevent falling victim to DNS hijackers.
1. Practice good cybersecurity hygiene
Avoid clicking on unknown links, as they might lead you to malicious sites or download malware on your computers.
2. Install a reliable antivirus software
You might unintentionally download malware that alters DNS settings in your device. Antivirus software scans, isolate, and remove these dangerous programs before they cause severe damage.
3. Be alert when visiting websites
Man-in-the-middle attack is hard to spot. So, be aware of slight changes in websites you frequently visit, particularly financial ones. Make sure that the URL is authentic and does not contain misspellings or other oddities.
4. Run a routine check on routers
Go to your router’s DNS settings and check if there’s anything amiss. Also, change the password at specific intervals as a precaution.
5. Use a VPN
VPN encrypts data and hides your IP address. It prevents ISP spoofing and stops hackers from intercepting the data. Some DNS attacks target unsuspecting users using public WiFi, which is unsecured and more vulnerable.
I use ClearVPN to ensure a secure connection, particularly when working in public spaces. ClearVPN’s military-grade encryption prevents unknown parties from spying on my data. Moreover, TechRadar recommends ClearVPN as a secure solution for web browsing.
FAQs
Can VPN prevent DNS hijacking?
A VPN can prevent DNS hijacking to a certain extent. Some attacks involve spying and intercepting the device data, and a VPN stops that. By encrypting the connection, a VPN makes the data unintelligible to hackers which will prevent DNS hijacking attempts. However, a VPN will not prevent malicious redirection if the hacker has tampered with the target web server’s DNS configuration.
What happens if your DNS is attacked?
DNS attacks might result in monetary losses. For example, users are tricked into revealing banking credentials on a fake website, which hackers use to access the users’ funds. In less damaging cases, you might be annoyed by inappropriate ads or blocked from accessing certain websites.
How to protect against DNS hijacking trojan?
A DNS hijacking trojan is malware that infects computers and changes their default DNS settings. Use anti-malware to detect and remove these malicious programs from computers.